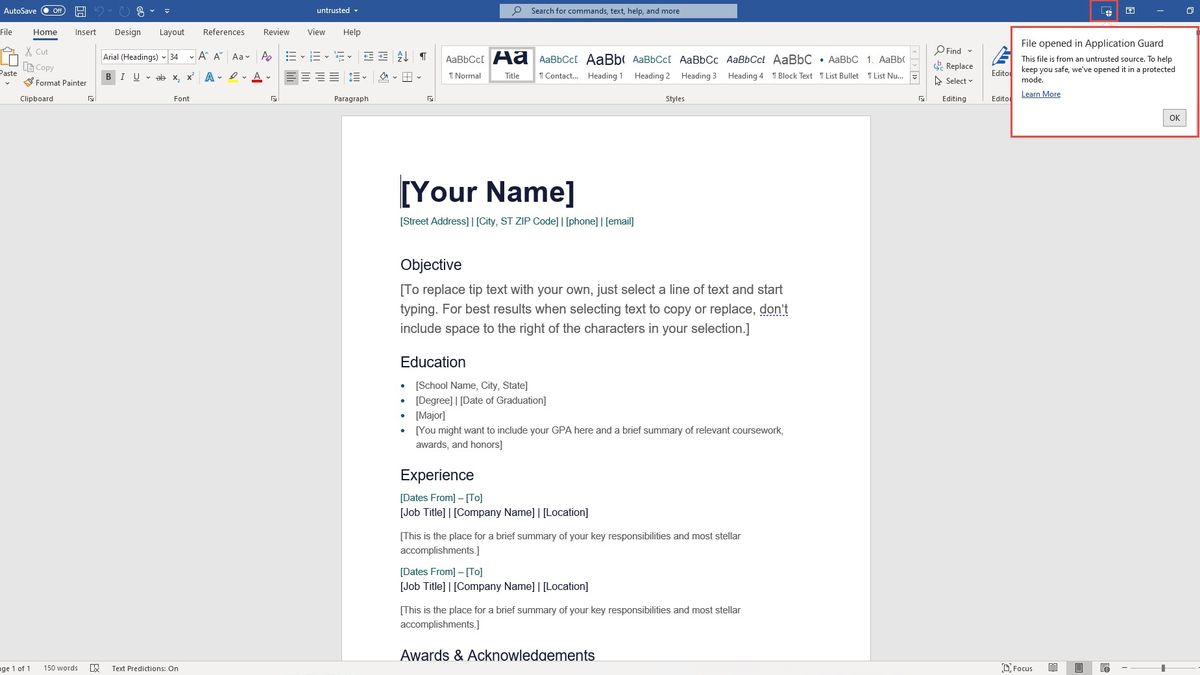
Malicious attachments are often used by cybercriminals as a means to gain access to an organization's network which is why...
attachments
After adding a Wi-Fi worm module to hack wireless networks earlier this year, the operators of the Emotet malware are...
After adding a Wi-Fi worm module to hack wireless networks earlier this year, the operators of the Emotet malware are...
Cybercriminals continue to devise new ways to deliver phishing emails to end users and the Cofense Phishing Defense Center (PDC)...